At the beginning of this week, several commentators rediscovered facts about the “unmasking” of Americans that we have known for more than two years. The public was afforded specific notification of the facts in an order issued by the chief judge of the FISA court, Rosemary Collyer, in April 2017. That order was released in redacted form. The order was issued in response to a report made by NSA’s Admiral Mike Rogers in October 2016, outlining abuses of FISA data pulls that been rampant for several years.
Although several bloggers wrote about it at the time (including related treatments I did of the topic of unmasking in 2017), the prospect of Attorney General William Barr being allowed to declassify agency records on this matter has raised it to new prominence. Independent analysts could suggest in 2017 that we needed an investigation and answers. With Barr’s authority signed by President Trump, we now have the possibility of getting those answers.
The specific catalyst for this week’s wave of interest appears to be a radio interview attorney Joe DiGenova did recently (embedded below). In it, he points out something we already knew: that the rash of “unmaskings” of Americans goes back to 2012. Sara Carter posted a report on the same point on Tuesday, 28 May.
Unmaskings done in the manner rebuked by the 2017 FISA court order were not the only ones done on members of the Trump campaign. It is important to emphasize that. Readers should understand that what started in 2012 was just one method of “unmasking” Americans, and was essentially an unauthorized one – which was why Admiral Rogers changed processing rules to put a stop to it on 18 April 2016. (It’s also why Rogers investigated what had been going on and reported it to the FISA court in 2016.)
The ability of senior officials in the executive branch to continue formal, authorized unmasking was not at issue in that rules change. The remarkable number of recorded unmaskings done by Susan Rice, James Clapper, and Samantha Power, and especially their reported connection to Trump and his associates, is a separate concern.
The central issue in the rash of unmaskings between 2012 and 2016 is a different one (although it probably involved staffers on the National Security Council, and in the FBI and CIA, who may also have been executing the formally recorded unmaskings for their bosses).
The central issue is about people with clearances and computerized access to identifying information about Americans running queries against the NSA-brokered communications database: queries designed to obtain identifying information through what we can basically call the back door.
Such queries are collectively called “Section 702 ‘about’ questions,” and refer to queries performed under the authority of Section 702 of the Foreign Intelligence Surveillance Act (FISA) of 1978. They are “non-contents” queries, meaning that they search for metadata on a communications event (e.g., a phone call, text message), but do not retrieve the contents of the communications. What metadata tells the user, however, is often quite enough: who is in contact with whom, date and time, which elements of the IT infrastructure the comms event was processed through (cell towers, ISP servers).
Without getting too eye-bleedingly into the weeds, the key thing to remember about the queries is that an analyst is supposed to query only for the database information he needs to fulfill his legitimate purpose. Most of the time, the objective is to develop the comms profiles of foreign targets who have no expectation of 4th Amendment protections. The agency analysts aren’t supposed to fish around for identifying information on U.S. persons when they’re running the queries.
When U.S. person participation in a foreign target’s comms profile is observed, there are protocols to be found in pursuing that further. What is not supposed to be done is running queries that masquerade as innocent, foreign-target queries, but are actually designed by their search terms to retrieve identifying data on U.S. persons.
The latter is what was happening in the Explosion Era of suspicious Section 702 “about” queries between 2012 and 2016.
Technological feasibility
How it became possible to do this in an automated, ill-policed manner is what I discussed in my “explainer” article in August 2017. I recommend reading it if you’re not up to speed on why the Obama administration’s intelligence community was able to foster the development of such an explosion. It took a technological transformation to enable it, and that was important in terms of both timing and the policy decisions behind it.
But in this article, we need to focus on the other aspects of the unmasking explosion. They are relevant to Spygate in more ways than one. They don’t just illuminate how the Trump campaign was spied on. The implications that go with them illustrate how John Brennan and the British could have been connected to the whole thing.
Before diving into that, see below one defining illustration of the scope of the 2012-2016 unmasking explosion. In 2017, the Office of the Director of National Intelligence (ODNI) published a summary of information relating to the revelations from the Collyer order in April. The ODNI report was intended as a good-faith statement to the public, recognizing the problems highlighted in Collyer’s order. Many readers have probably seen this little graphic before but might not have fully realized its import.

(ODNI transparency report graphic)
That’s the smoking gun. It was evident to those of us writing in 2017 that the graphic meant spying on Americans went off the charts, starting between 2012 and 2013 and accelerating after that. Now the rest of the public has enough information under its belt to see the same thing.
The rest of the 2012 story
It wasn’t only the automation and poor policing within the IC that made 2012 the starting line for the unmasking explosion.
I wrote about this in early April 2019. The 2012 event at issue was a motion to the FISA court brought by the Department of Justice, which would expand the sharing among federal agencies of the intelligence collected under FISA authority.
Again, I commend this earlier post to your perusal, rather than rehashing it here. The short version is that the main focus of the 2012 motion was lubricating a data-sharing agreement between the FBI and the National Counterterrorism Center (NCTC).
The driving factor behind the request to the FISA court was ostensibly the failure in December 2009 to detect in advance the intentions of a known terrorist sympathizer: the infamous “Underwear Bomber,” Umar Farouk Abdulmutallab. Fortunately, although he got onto his transatlantic flight with explosives in his underwear, Abdulmutallab was prevented by the quick reactions of other passengers and the aircrew from actually setting them off during the trip.
But afterward, the Obama administration concluded that U.S. federal agencies needed the ability to share sensitive information more broadly among themselves, including information on U.S. persons with 4th Amendment rights.
The DOJ motion was granted, and the broader, automated data sharing that enabled the NCTC to access more from the FBI’s information on Americans was implemented.
It was in the period after this measure was instituted that Section 702 “about” queries began to explode. The specific procedural changes that may have allowed that aren’t fully visible to the public. But the timing is unmistakable.
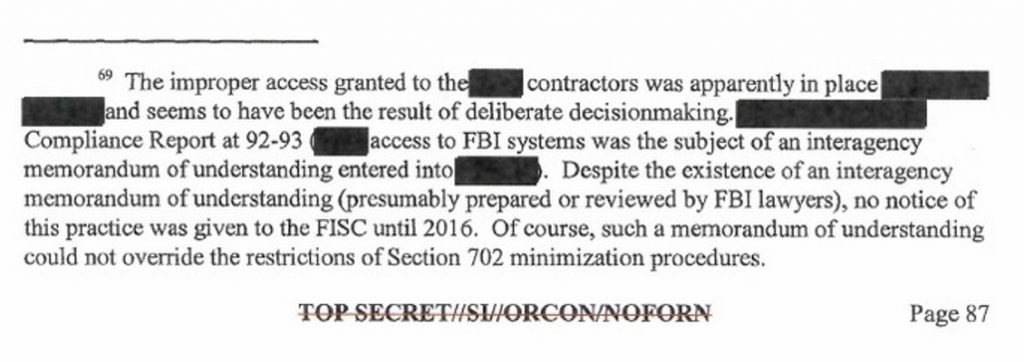
We come at this point to a matter of central relevance to 2012 as the dividing year, and that is how the data-sharing change just described relates to one of the critical findings of the 2017 Collyer order. That finding is that a contractor for the FBI – its name redacted for public release – was being allowed to improperly access unminimized (i.e., unmasked) data on U.S. persons, and had been for some time.
Although I had written about that before (e.g., as probably the big blow-up at the FBI’s Washington Field Office referred to in a 9 March 2016 text message from Lisa Page to Peter Strzok), I didn’t discuss it concerning the 2012 request, in my 7 April 2019 article.
I didn’t do so because my emphasis in that article was on a connection with John Brennan. And at that point, seven weeks ago, the case wasn’t as strong as I believe it is now that Brennan is a link to that factor as well as others.
Enter Brennan
But from the perspective of recent revelations, on which more below, it appears increasingly likely that the contractor whose name is redacted in the Collyer order was the company Brennan was the president of between 2005, when he left the Terrorist Threat Information Center (TTIC), and 2009, when he joined the Obama administration. The company was called The Analysis Corporation.
There is much more detail, and several informative links, in my 7 April post; please see it for the background. The Analysis Corporation, or TAC, was one of the numerous contractor companies that provide analysis and IT services to federal agencies. Brennan’s role with it, as president from 2005 to 2009, had amplified significance in this scenario for two reasons.
One is that Brennan honchoed the Obama administration’s reaction to the Underwear Bomber problem. He was the counterterrorism “czar” in Obama’s Oval Office who approved and shepherded the policy push for the expanded intel sharing on Americans.
The other is the TAC contracting history I laid out at some length in the 7 April article. Noting that TAC had become a subsidiary of the contracting company Sotera by the time of these events, here is the gist of the contractor nexus:
Sotera (at that point still doing business as TAC) went on to be awarded a major contract with the NCTC in November 2008 – a contract for “integrated analytical and operational support services.” In other words, the contract was to provide analysts for the NCTC, which is largely staffed by civilian contractors. Sotera has continued to provide contract analysts to the NCTC in the years since.
Brennan was still the president of TAC at that point; the date of the contract press release was less than three weeks after the election.
The third event occurred in October 2009, when a post-Brennan TAC won another contract: this one to “provide operations and maintenance (O&M), user support and product development for the Federal Bureau of Investigation’s (FBI) Investigative Data Warehouse (IDW).”
TAC thus had contractor personnel embedded in both agencies, with access to their sensitive databases full of intelligence and operational information.
Given that the purported purpose of the 2012 data-sharing motion was to facilitate information flow between the FBI and NCTC, the centrality of TAC’s position in that regard was probably unmatched. TAC had contract personnel embedded in the day-to-day operations of both agencies, working on the same body of data and processes.

Don’t even think about it. Guard gate at the National Counterterrorism Center (NCTC) in McLean, VA. Google Street View
It is for that reason that I suggest Brennan’s TAC – doing business by 2009 as a subsidiary of Sotera – is the contractor referred to in Judge Collyer’s order.
In particular, I think TAC makes the most obvious candidate for the contractor alluded to in a footnote which our colleague “Sundance” at Conservative Treehouse has highlighted on several occasions.
It’s essential to shout out to Sundance and the tremendous work done for months in parsing the Collyer order and focusing attention on the mysterious contractor. I’ve drawn a different conclusion from the beginning about who the contractor is likely to be. But Sundance has posed the proposition about the contractor’s role that, for me, frames it as TAC.
Here’s how Sundance put it in a new article posted on 28 May (italics in original):
Note the phrase: “([redacted] access to FBI systems was the subject of an interagency memorandum of understanding entered into [redacted])”. This sentence exposes an internal decision; withheld from congress and the FISA court by the Obama administration; and outlines a process for access and distribution of surveillance data. Note: “no notice of this practice was given to the FISC until 2016“.
The implication of an MOU formality between the agencies, specifically related to the unnamed contractor, makes a contractor who we know was involved in precisely the processes we’re talking about – at both agencies – the most likely one.
That would be TAC.
In hindsight, what appears to have happened between 2012 and 2016 was that contract personnel had user credentials on classified IT systems that enabled them to query for identifying information on U.S. persons – and that that arrangement was made in an MOU between the FBI (or DOJ) and NCTC. (Note that NCTC is subordinate to ODNI.)
But, as Sundance emphasizes, the FISA court wasn’t told about the arrangement at the time, and only found out about it when Admiral Rogers reported to the court on his investigation of Section 702 cases of abuse.
If any company in America was in a position to be the contractor involved, it looks like TAC.
I’ll also take a moment here to recommend reading the rest of sundance’s 28 May article. It makes a compelling case that the 2012 FISA motion could have served to facilitate the “Secret Research Project” involving the IRS that Obama’s DOJ, under Eric Holder, was running on targeted Americans. That possibility fits elegantly in terms of timing, although the formal justification for the motion to the FISA court was the counterterrorism data-sharing issue highlighted after the Underwear Bomber event.
A link to the IRS targeting is undoubtedly feasible. I would suggest Barr and his delegate, U.S. Attorney John Durham, need to look at the whole scope of possibilities. Whatever the depth and breadth of them, those possibilities have grave implications not only for the spying on the Trump campaign but for the unconstitutional targeting of all Americans.
In either case, Brennan’s old company, TAC, looks like the contractor most probably involved.
The British connection
There are too many dimensions to the British links of Spygate to try to cover them in one post. I will restrict myself here to a couple of connections that relate to Brennan’s company, TAC.
Before doing so, we must note that an essential impetus for inspecting the 2012 motion to the FISA court came from Rep. Louie Gohmert (R-TX), who – as observed in my 7 April article – expressed concern that that motion itself facilitated alleged UK involvement in pulling surveillance data on Americans. In some aspects of the framework for doing that, Gohmert may not be wrong.
But the TAC link is what I want to highlight here. In pursuing it, the first thing to know is that when TAC was bought by Sotera in 2007, it came under the ownership of a British parent company, Global Strategies Group, through a subsidiary called GTEC. I refer you to the 7 April article for extensive background on this.
Global Strategies Group was founded by Damian Perl, a former Royal Marine, and former Scots Guards officer Charlie Andrews. The hint of swashbuckling in this corporate provenance has tended to overshadow a point more relevant to the current discussion, which is that GSG has acquired some executives with extensive CIA histories, and had two around the time the TAC contracts with the FBI and NCTC were initiated, and the 2012 FISA motion was brought.
One of the officers was John Gannon, who would have known Brennan in the 1990s when both were senior officials with the CIA’s intelligence directorate. Gannon was the CIA’s deputy director for intelligence from 1995 to 1997, responsible for preparing presidential briefs; Brennan was reportedly a daily briefer for Bill Clinton during a portion of his presidency and was the chief of station in Saudi Arabia at the time of the Khobar Towers bombing in 1996. Gannon joined GSG’s board in 2012.
The other was CIA veteran Jack Devine, whose connections are of greater significance on the British side. Devine was, to begin with, added to the board of Sotera parent company GTEC, the GSG subsidiary, in 2007, the year Sotera bought TAC. He and Brennan may not have known each other well during their CIA years; Devine is somewhat older and from a different generation. But they would have known of each other and encountered each other through the Sotera-GTEC connection.
More important are two features of Devine’s career that would have brought him in contact with the constellation of British intelligence officials lurking around Spygate. The first is that Devine was the chief of station in London from 1995 to 1998. (See the link above, as well as here and here.)
The London post is a prestigious one, entailing connections with the intel establishment of one of America’s closest allies. Besides interacting with personalities like John Sawers and Richard Dearlove, Devine probably had contacts with a British intelligence official who has surfaced in recent weeks as someone briefed on the Steele dossier in 2016, and who probably conveyed information about it to Theresa May.
That individual was the late Charles Farr, who sadly passed away in February 2019 while serving as the head of the UK’s Joint Intelligence Committee (JIC), a cabinet-level body somewhat analogous to ODNI in the United States.
In the 1990s, from 1995 on, Farr was an undercover officer for MI6 stationed in London, according to the always-stellar research done by Twitter user “Undercover Huber” (@JohnWHuber)
The only person who fits both is FARR. A leaked list of from MI6 confirms he *was an undercover MI6 officer*, based in London between 1995-2006. Chris Steele was also posted undercover to London at this time, 1993-1998. Their MI6 positions AND locations overlap for at least 2 yrs pic.twitter.com/aRLN0wq8xJ
— Undercover Huber (@JohnWHuber) April 25, 2018
While Christopher Steele was also in London at the same time (see Huber thread), and Devine may well have met him, Devine and Farr had a unique prior connection. Whatever duties Farr was performing in the 1990s, Devine was likely to be in contact with him in London, as both had been intimately involved in running operations in Afghanistan in the 1980s, during the Soviet occupation.
Devine was a seasoned CIA operative at the time, whereas Afghanistan was one of Farr’s earliest postings in MI6, according to the public information about him. The two were nevertheless unusually likely to have crossed paths because of that common operational link.
In a related and thought-provoking twist, given TAC/Sotera’s role with the NCTC and counterterrorism analysis in the 2000s, Charles Farr was also intimately involved in the counterterrorism portfolio in the UK, at the same time TAC’s connection with the NCTC-FBI-2012 drama was developing. Farr had moved out of MI6 in 2006, and from 2007 to 2015, he was the head of the Home Office’s Office of Security and Counterterrorism (OSCT).

Charles Farr. Via Daily Mail; video screen grab
Thus, Farr – who had a history that intersected with GSG executive Jack Devine’s – was at the pinnacle of the UK’s counterterrorism business when GSG subsidiary Sotera bought Brennan’s TAC (2007); when Brennan was in the counterterrorism “czar” role in the White House under Obama (2009-2013); and when Brennan moved on to become CIA director in 2013.
In his stint in the Home Office, Farr worked for Home Secretary Theresa May from 2010 to 2015. Reportedly, the two had a fiercely loyal working relationship, which would color any long-distance assessment of how much Farr may have told Prime Minister May in 2016 about the Steele dossier caper in the U.S.
But one other factor may tell us more. Farr, who never married, was in a romantic relationship with May’s closest aide, Fiona Hill (Cunningham). An inter-ministerial dust-up in 2014 resulted in that year in Hill’s departure from May’s staff – but Hill’s relationship with Farr continued until his death, and in fact, was remarked on by the obituary articles in 2019. When May became prime minister in 2016, after David Cameron’s epic Brexit loss, Fiona Hill returned to her staff and has remained on it. (May, of course, will depart her post now on 7 June with a new election to follow.)
In light of these details, is it likely that Charles Farr’s information about the Steele dossier in 2016 got to May in a timely fashion? You tell me.
One other point of note: Jack Devine was the chief of station in Rome before he was posted to London (see links above).
No, make that two. GSG sold its Brennan-linked properties before Brennan was nominated to be CIA director. But GSG continued to seek government contracts in the U.S., and in 2013 hired the Podesta Group to represent it.
The obvious implication
In a puzzle like that of Spygate, which has key personnel pieces (e.g., Brennan), key system and policy pieces (e.g., FISA surveillance), and critical factors like the involvement of other particular nations (e.g., the UK), it is extremely rare to encounter sub-storylines having all those pieces, and not find that they are both related and explanatory.
It is really, really likely that it matters to the 702-queries Explosion Era of 2012-2016 that Brennan’s old company, TAC, had precisely the federal contracts necessary to be a key participant in the explosion. Brennan’s links to the surveillance of the Trump campaign, and his involvement in fanning the smoke of the Russiagate narrative, just make it even more likely.
The British connections through TAC pile more likelihood on top of that.
Spygate did start in 2012, in terms of a critical form of the spying. And John Durham should have some excellent clues at this point where to look.
Cross-Posted With Liberty Unyielding